Advanced solutions
Prepare your organization toward cyber risk by analyzing your maturity level and implementing improvement projects
Security assessment
Companies could waste time, effort and resources in implementing measures to protect against unlikely events. Via a security assessment using ISO 27001 framework, you can receive a report highlighting gap analysis versus your IT security targets as well as a roadmap to follow with prioritization advice.
Managed vulnerability scan
The constant evolution of IT architectures and cyber threats makes more complex the identification of knows vulnerabilities with systems and assess the associated risk level. Constantly scan your IT infrastructure and systems to identify vulnerabilities within your perimeter. Receive regular report summarizing the vulnerabilities identified as well as a suggested remediation plan.
Penetration testing
It might be complicated for a company to have a good control over infrastructure protection. Adopt a punctual offensive approach to identify and exploit vulnerabilities (internal, external, applicative) in your cyber security defences and detection to provide recommendations and remediation plan.
CISO as a Service
Implementing IT security projects can sometimes be difficult for organization without dedicated resource on the topic. Requesting a CISO as a Service allows organizations to launch IT security initiatives in a flexible and delivery oriented way.
Protect your entry points to avoid intrusion in your systems threatening data privacy and business continuity
Network
Networks are extending drastically due to broader enterprise perimeter. As a consequence, vulnerability risk is stronger than ever and network protection and security is becoming more and more complex. Select solution bundle (NGFW, Email, VPN, NAC…) to match your needs.
PC & Laptops
Endpoints have always been critical assets to protect within an organization as directly exposed to human errors. With our new generation endpoints protection solutions (AI & Machine Learning), confine threats coming from endpoints while offering the best experience to your users.
Mobile Protection & Management
Growth of mobile data consumption and enterprise applications’ access on mobile position smartphones as a new vulnerability in the security perimeter. Thanks to our mobile security solutions Mobile Threat Protection and Mobile Device Management,you can keep control on your mobile fleet.
Identity Access Management
Segmenting information access within an organization is an efficient way to restrain the security risk. Delivering such project can be technically complex and time consuming. Benefit from our expertise in the domain to support your IAM initiative.
Detect anomalies in your infrastructure or application to be able to undertake appropriate corrective actions
Managed Infrastructure
Managing security and connectivity equipment requires time, resources and expertise. Outsourcing these activities is a good way to benefit from in-depth expertise in the domain while you can focus on your core business. Take advantage of our competences and local infrastructures (SOC) to manage your equipment.
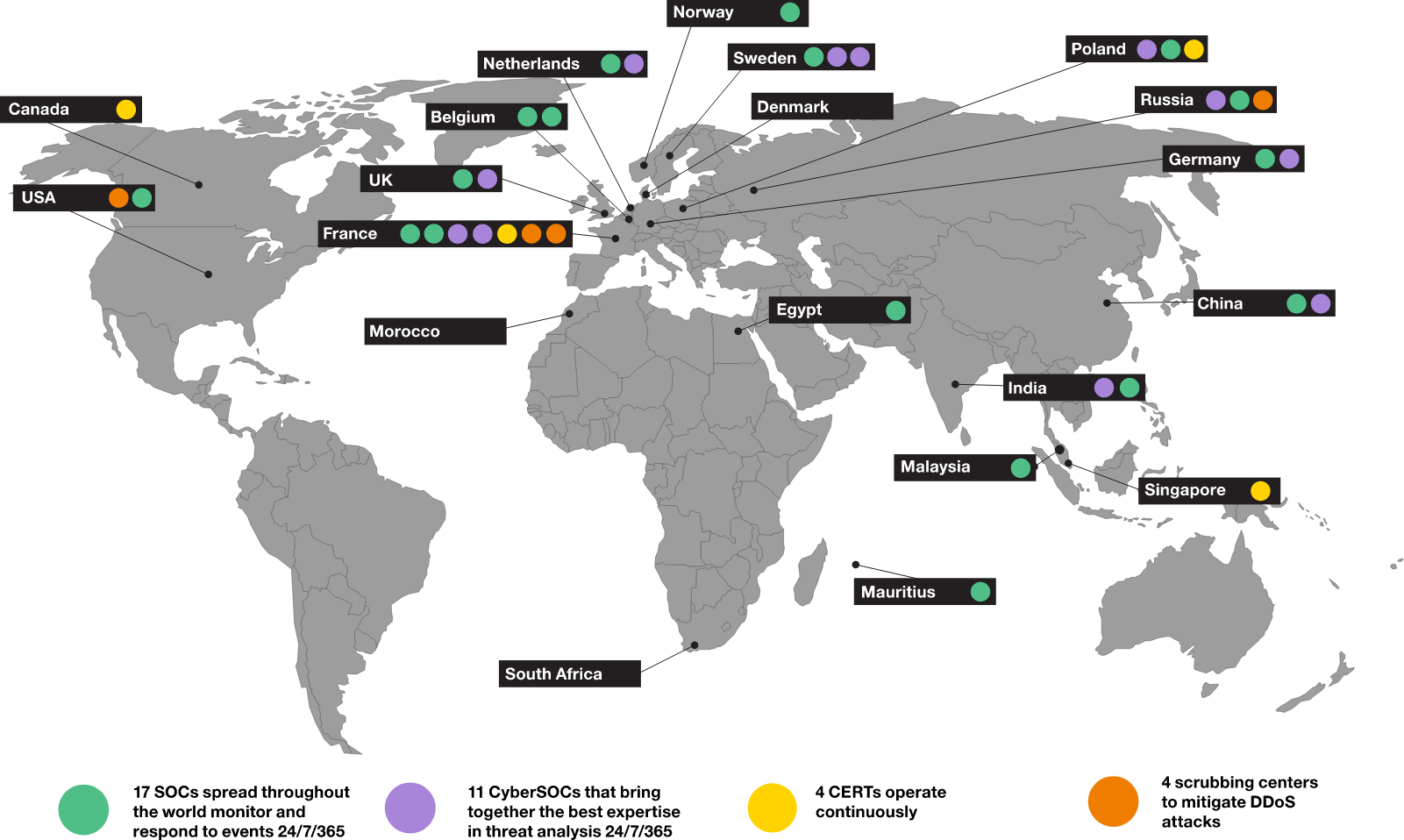
Cyber SOC
Implementing a SIEM platform allow you to collect and gather security events generated within your infrastructure (system, equipment, applications). The latter are then categorized and analysed to generate alerts according to criticality levels. Orange Cyber SOCs located across the globe ensure real time monitoring to support you 24/7.
Advanced SOC
Real time analysis of the security alerts generated by protection equipment requires putting in place a dedicated operational model, sometimes difficult to implement and support on long term. In the meantime, detection and response capacities become predominant in every security strategy. Orange can support you in security event management by centralizing all your alerts within one of our SOC (24/7). Our specialists will take care of alerting you in case of incident and providing regular reporting of the events and alerts recorded.
Application security
Application code can be numerous within development processes. Some of these bugs can hinder application availability. Possessing a certain expertise in the domain, Orange accompany you in securing your applications according to 3 levels: 1/ Consulting & Advisory 2/Technological solutions 3/ Service Management
React appropriately to a cyber security incident affecting your IT system
Cyber Emergency Response Team (CERT)
Request support to our CERT to provide you with expertise and technical advice in cyber security incident management. Positioned as a central component of your incident response strategy or backing your internal team, our experts can help you at every step of incident management.
In case of emergency, you can contact Orange experts via the hotline at +32 3 808 21 92.
Anticipate future event and increase your organization resiliency
Awareness program
In every organization, employees remain, despite their willingness, the weakest link facing cyber risk. Raise awareness among you team over risks they are exposed to and allow them to adopt the good reflexes.
Security exercises
Once your cyber security strategy is in place and awareness has been raised within your employees, test their reaction capacity in organizing Phishing simulation exercises. Our solutions offer several approaches adapted to your environment to make the exercise as representative as possible.
Digital Footprint
Your attack surface might be broader and your organization more exposed than you imagine. Highlight your exposition on the “Dark Web” as well as possible data leak related to your brand and domain names thanks to a specialized security application. Our experts will provide you with a synthetic report of the results observed as well as some recommendations to improve your security posture.
Basic solutions
Mobile
Benefit from a standard mobile protection with F-Secure Mobile Security included in our Connected Mobile tariff plans.
PC & Laptops
Equip your PC & laptops to protect your endpoints against cyber risks.
Network
Protect your network from internet threats using our shared firewall.
Benefit from standard firewall included in our Connected Internet routers.
Why should you entrust your security to Orange?
Orange group is a European leader in cyber security with particularly leading position in security management services (MSSP)
Solutions to support Belgian companies in 3 main cyber security domains:
Local experts dedicated to our Belgian clients :
A unique partner to provide you with connectivity and security as a 1-Stop-Shop.
Interested Get in touch with us
Would you like us to help you implement our solutions ?
Take a moment to fill in the contact form.
Our experts will contact you shortly to answer all your questions.